As I explained in a previous post I had to demote my Active Directory domain at home which effectively destroyed the domain and the OU structure with it. Fortunately, with a bit of advanced planning I managed to retain the structure by exporting the OU structure and then importing it into the new domain.
I briefly covered how I done this earlier in that post but that was more in note form. Hence, I wanted to write a quick how-to post on this subject separately, which uses the ldifde.exe tool for the export and import task.
Exporting the OU Structure
ldifde.exe is a simple command line tool which can export the OU structure in a text file., which needs to be run on the actual domain controller.
As an example, this is how the export command should look like:
ldifde -f c:\ExportOU.ldf -s winserverdc.emeneye.co.uk -d "dc=emeneye,dc=co,dc=uk" -p subtree -r "(objectcategory=organizationalUnit)" -l "cn,objectclass,ou"
Change the following in the above example to suit your environment:
- The location and name of the export file (C:\ExportOU.ldf)
- The domain name Name of the domain controller in which the command is being run on (Winserverdc.emeneye.co.uk)
- The domain name (“dc=emeneye,dc=co,dc=uk”)
You can execute the command as a Run Command or in a batch file, which will produce an ExportOU.ldf file (in the root of the C: drive in our example above).
Back up the ExportOU.ldf and store it in a safe place. You’ll need this later on when you’re ready to import the OU structure in a new domain.
Importing the OU Structure
You will need to edit the ExportOU.ldf file before you can import the OU structure in the new domain, as follows.
- Remove the first entry which references the domain name. We need to remove this because the domain name cannot be imported and without removing it the import command will fail
- Replace all occurrences of the old domain name with the new domain name
When that’s done you’re ready to import the OU structure in your new domain.
Again, an example of how the import command should look like is provided below:
ldifde -i -f "C:\ExportOU.ldf" -s winserverdc
As before, change the following to suit your environment
- The location and name of the export file (C:\ExportOU.ldf)
- The hostname of the domain controller in which the command is being run on (winserverdc)
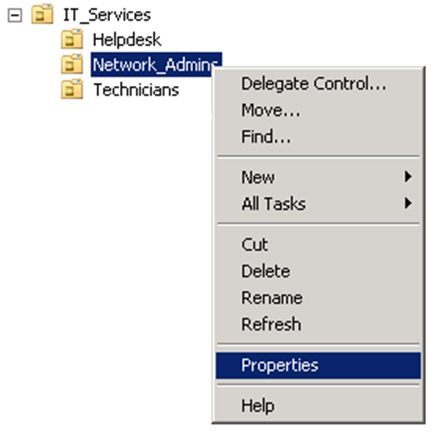
If all goes well the command will have successfully imported the OU structure in the new domain. Launch the Active Directory Users and Computers console to verify.